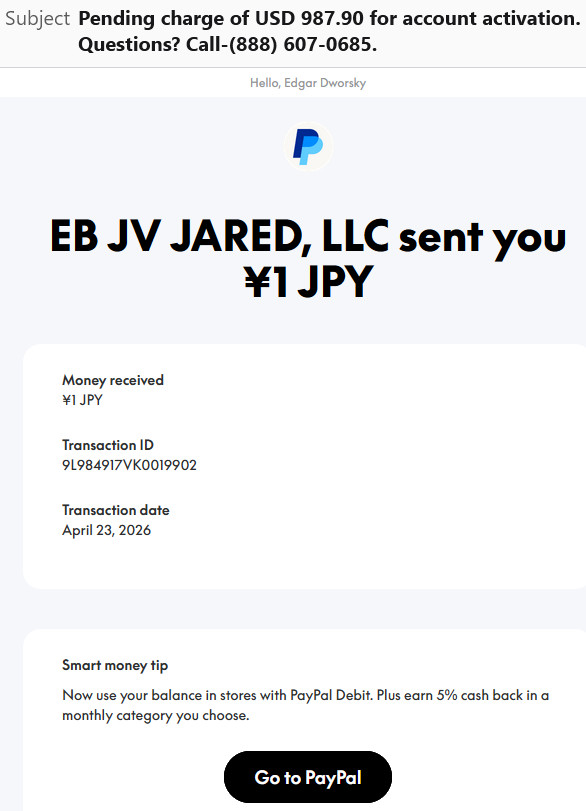
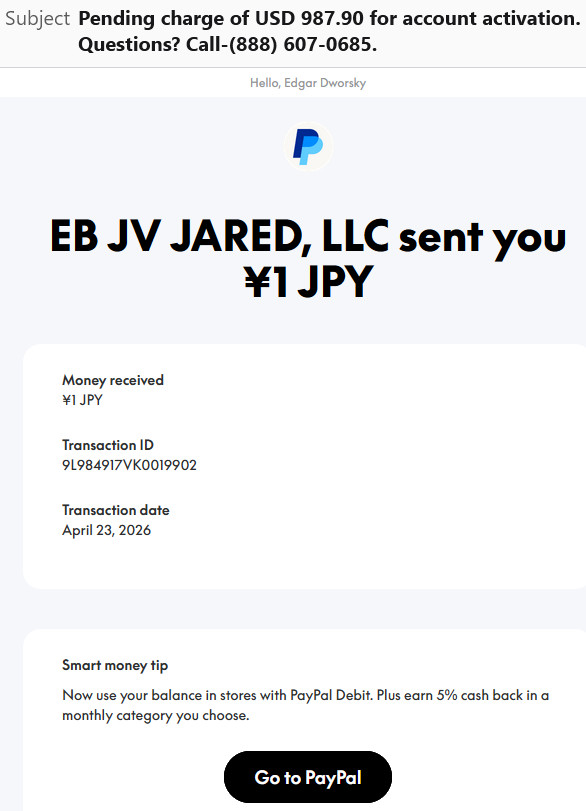
MrConsumer received this email last week, indicating that there was a pending charge of almost $1,000 on his PayPal account and that a deposit had also been made to it:
While normally I would merely click the junk button in my email program when getting an email like this, I decided to look a little further.
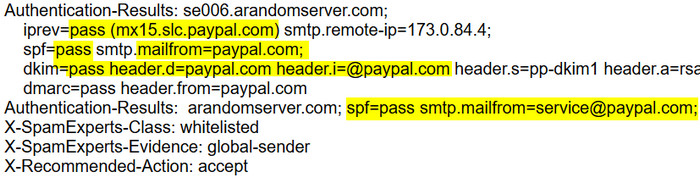
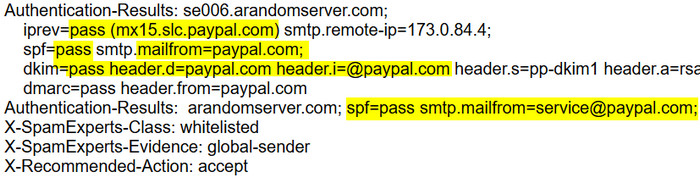
Checking the email header confirmed that PayPal was the actual sender.
*MOUSE PRINT:
Hovering over the “Go to PayPal” button revealed that the link was also to the actual PayPal site. Rather than clicking it, I went directly to PayPay in my browser to check on my account. This is what I found there.
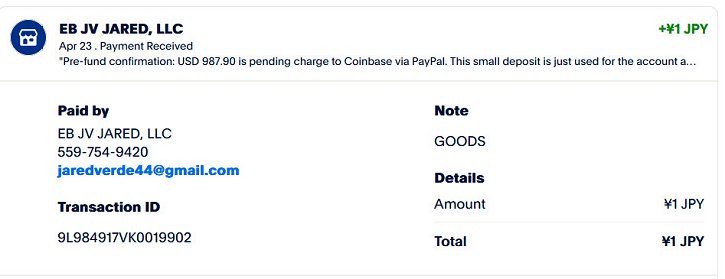
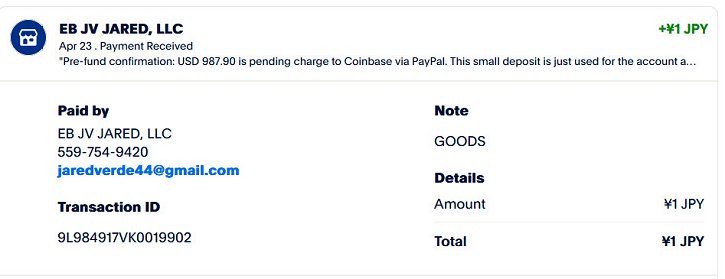
To my shock, the actual PayPal website said that there was a pending charge of $987.90 coming to my PayPal account. And it showed an actual transaction that was a test deposit into my account of one Japanese yen. Presumably this was to ensure my account was valid.
I immediately changed my password, and searched the PayPal site to dispute the forthcoming charge. Entering information about the actual transaction that was there — the one yen deposit — resulted in an error indicating that that transaction could not be disputed.
So I called customer service at PayPal using a number I had in my rolodex (888-221-1161) and NOT using the number the email had provided to dispute the transaction. (That step was key so as not to fall for any possible scam.)
After being forced to go through a number of AI prompts to direct my call, I was finally able to speak to a real person. She indicated that I had nothing to worry about — a fraudulent charge was not about to be deducted from my account. She said this was a phishing scam that they were aware of and that it used a real link to PayPal as part of the deception.
The one yen test deposit was a means of making the transaction look legitimate. That action forced PayPal to send me a real confirmation email, and to list the transaction on their website.
But how did the scammers get PayPal to also communicate that a nearly $1,000 charge was pending? It seems that some senders of money like these scammers can put whatever message they want in the subject line or the body of the email that PayPal sends to recipients of money. It will also appear on the PayPal website.
So for one yen, which is worth a little more than half a cent, the scammers can make their pending charge look legitimate and trick people into calling their own 800 number. Clever. Very clever.
A word to the wise… if you get a similar email, do not under any circumstances call the 800 number shown. But you can contact the real PayPal to check on the legitimacy of the transaction posted. And do forward a copy of the email to them: Phishing@PayPal.com
Here are some tips from PayPal to avoid phishing scams.

 Photo Illustration
Photo Illustration